In order to fully understand a company's security risks, we must first analyze the workflow of the sensitive data.
What is the Data Flow Analysis?
A thorough analysis of how an organization's users are utilizing their sensitive data in rest and in motion in ways that vulnerability scanning tools cannot detect. The purpose of this is to define boundaries for security responsibilities as well as confirm that data transmission is secure and protected from a compliance perspective.
Data Flow Analysis Phases
The Data Flow Analysis phase of the risk assessment is completed in two parts:
- Data Flow Questionnaires
- Typically sent to 30-50% of employees within the organization
- Designed to take approximately 10-15 minutes to complete by each team member
- Data Flow Interviews
- Interviews are conducted with 1-2 resources per department that store or transmit sensitive data. discovered in the questionnaire
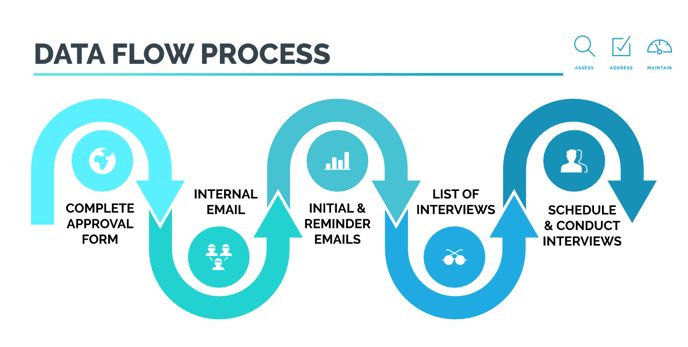
|
Client Approvals & List of Users |
|
|
| Internal Client Management Email |
|
|
| Choice Questionnaire Emails |
|
|
| List of Interviewees |
|
|
| Conduct Interviews |
|
|
| Data Review & Analysis |
|
Client On-boarding Responsibilities
- Gather a list of users that store or transmit sensitive data from each department
- 30-50% of your team, with a thorough representation of approximately 4 or more resources from each department
- We prefer a spreadsheet with first name, last name, email address & department
- Companies with less than 20 users: Please provide a list of all users
- Check Your Email to review and Complete the Choice CyberSecurity Data Flow Questionnaire Approval Form provided
- At the end of the questionnaire, you will be prompted to provide a list of participants and their email addresses
- Once approved, we will send another email with the Management Email Template and unique form for you to Send Management Team Email to all Questionnaire users
- Alert Choice team when email has been sent to begin our email process approximately 2 business days after your email has been sent
Please DO NOT send the Data Flow Analysis Approval Form to your users. The approval questions at the end will confuse them and it is not designed to collect results from more than one team member.
